NO.:TPSA20-12From:TSRCDate:2020-04-17
During the covid-19 outbreak, Tencent Meeting is providing free services and connecting users all over mainland China. Its international version, VooV Meeting, has been launched in more than 100 countries and regions around the world.
In order to meet growing needs, Tencent has continuously upgraded its key functions and services, and iterated and updated 20 versions within the past 100 days. To further enhance security, Tencent Security Response Center (TSRC) has decided to launch the " TSRC – Securing Voov Meeting" special project, calling on the researcher community to help us surface vulnerabilities and prevent the exploitation of unknown security risks.
【Project Duration】
17 April 2020, 18:00 (GMT+8) to 30 April 2020, 18:00 (GMT+8)
【In-Scope Assets】
1. Mobile Apps and Executables
• Tencent Meeting client (including macOS, Windows, iOS App, Android App, WeChat miniprogram)
• Tencent Meeting Server
2. Web Domains:
*.wemeet.qq.com
*.meeting.tencent.com
*.meeting.qq.com
*.voovmeeting.com
【Rewards】
1. For the “TSRC – Securing Voov Meeting” special project, TSRC has allocated a total of one million RMB bounty amount (approximately USD$140,000).
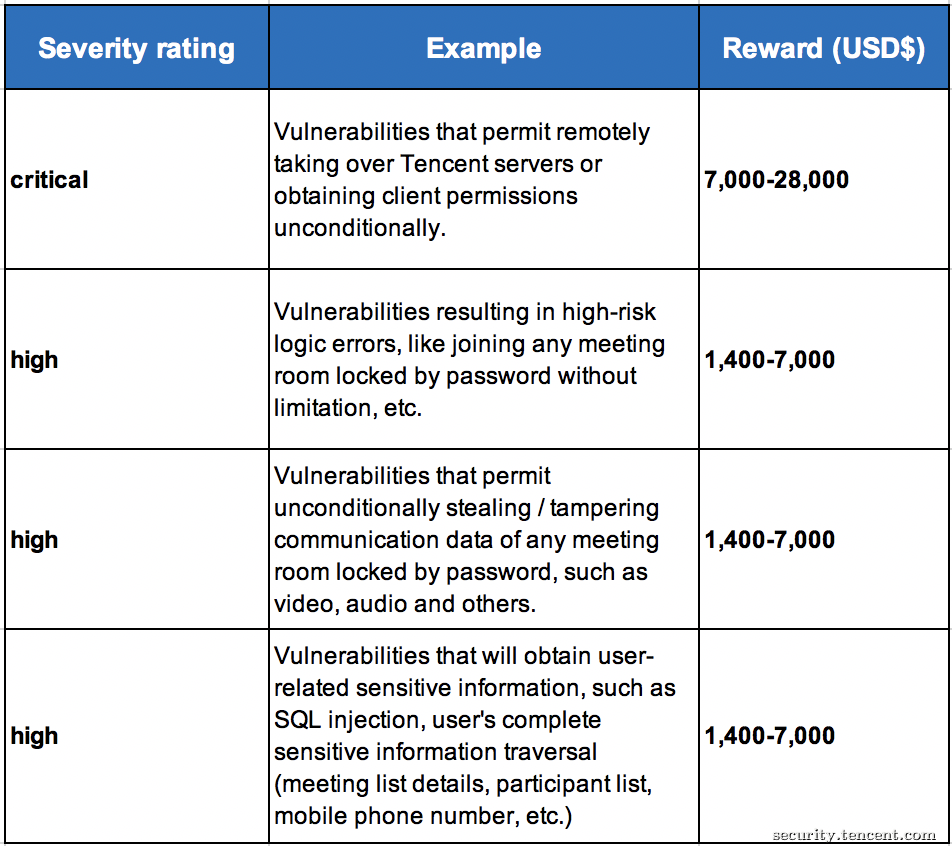
2. TSRC will be awarding bounties, ranging from USD $1,400 to USD $28,000, depending on the impact (critical/high-risk) of the vulnerability within the given scope. The table below details the rewards for this project-
3. Researchers reporting other eligible vulnerabilities not mentioned above will receive regular monetary rewards and credits as usual. Please refer to the Tencent policy page to view the regular bounty table.
【Report Submission】
Please note that all vulnerabilities reports must be submitted on TSRC (https://en.security.tencent.com/index.php/report/add), using a title starting with "[Voov Meeting]". If multiple researchers report the same vulnerability, the reward will be awarded to the first reporter.
【Rules of Engagement】
1. For Mobile Apps and Executables, a working exploit must be provided; for web domains and servers, a proof of concept enabling Tencent to efficiently reproduce the reported issue must be provided.
2. Vulnerability ratings will determined by CVSS and TSRC vulnerability scoring standards, indicated in the TSRC Bounty Policy.
3. Researchers are to read the terms indicated in the TSRC Bounty Policy. Please note that the usual bounty policy rules apply for this project.
4. If the researcher has any questions about the scope, submission process, vulnerability assessment and rating, etc., please use the comment function of your vulnerability report page or contact us at security@tencent.com directly. TSRC will protect the due rights of researchers, and if necessary, may bring in external parties to make a joint decision.
捐款成功,感谢您的无私奉献